SSO setup with ADFS
Setting up ADFS and SAML 2.0 with Kazoo!
Requirements
To use ADFS to log in to your Kazoo instance, you need the following components:
- An experienced IT or Systems admin with knowledge of how to set up ADFS SSO with third party platforms.
- An Active Directory instance where all users have an email address attribute.
- If your company plans to use our mobile app, the Active Directory instance will require configuration changes that allow for out of network access.
- A KazooHR subdomain.
- A server running Microsoft Server 2012. This guide uses screenshots from Server 2012 R2, but similar steps should be possible on other versions.
- ADFS Metadata url with a unique SSL Signing certificate.
After you meet these basic requirements, you need to install ADFS on your server if you have not already. Configuring and installing ADFS is beyond the scope of this guide, but is detailed in the Microsoft Knowledge Base.
When you have a fully installed ADFS installation, note down the value for the ‘SAML 2.0/W-Federation’ URL in the ADFS Endpoints section. If you chose the defaults for the installation, this will be ‘/adfs/ls/’.
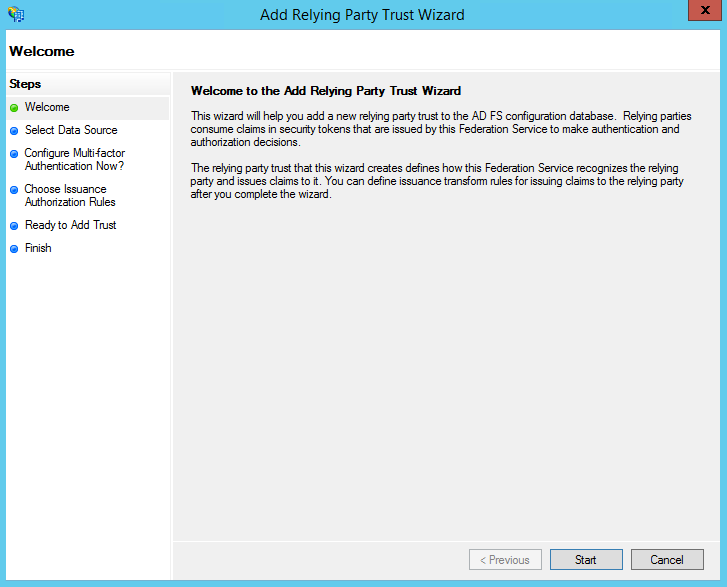
Step 1 - Adding a Relying Party Trust
At this point you should be ready to set up the ADFS connection with your Kazoo instance. The connection between ADFS and Kazoo is defined using a Relying Party Trust (RPT).
Select the Relying Party Trusts folder from AD FS Management, and add a new Standard Relying Party Trust from the Actions sidebar. This starts the configuration wizard for a new trust.
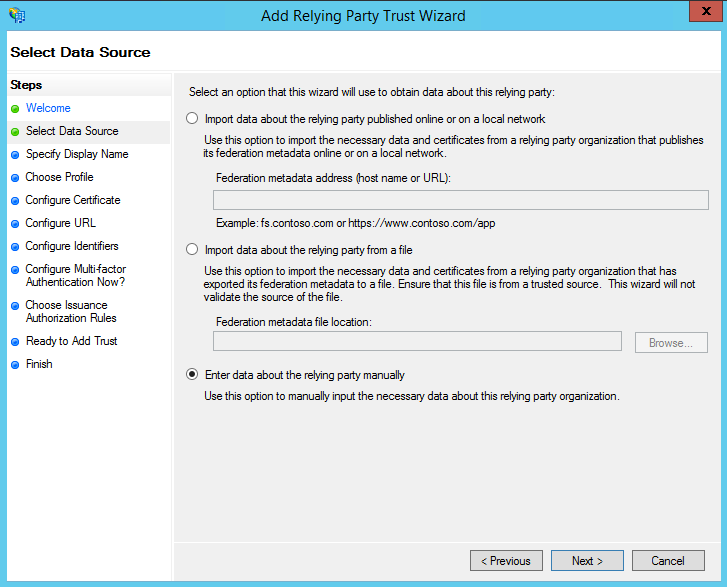
- In the Select Data Source screen, select the last option, Enter Data About the Party Manually.
- On the next screen, enter a Display name that you’ll recognize in the future, and any notes you want to make. Make sure this is Kazoo relevant (i.e. Kazoohr Login)

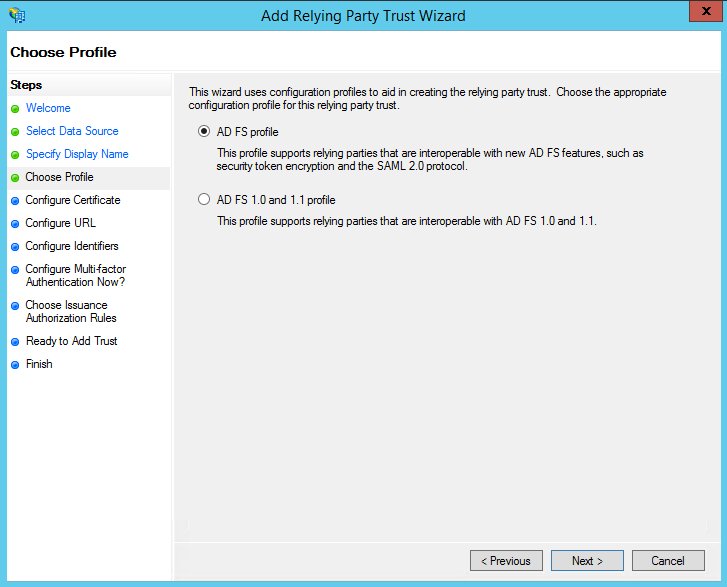
- On the next screen, select the ADFS FS profile radio button.
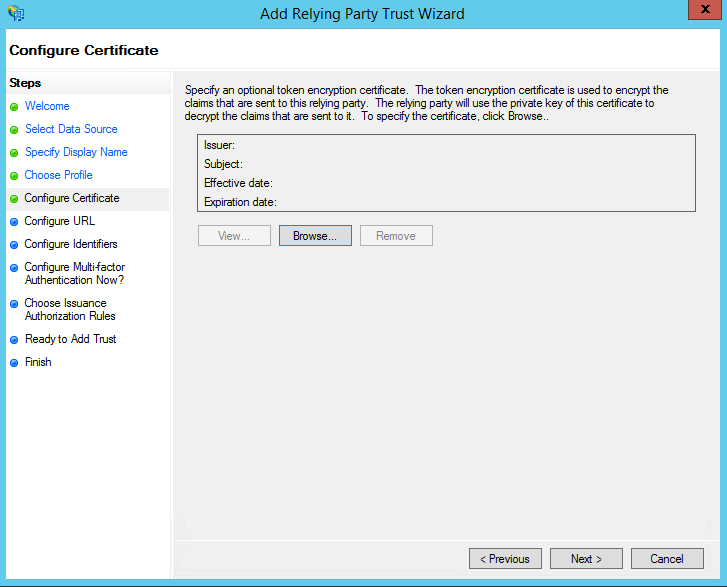
- On the next screen, leave the certificate settings at their defaults.
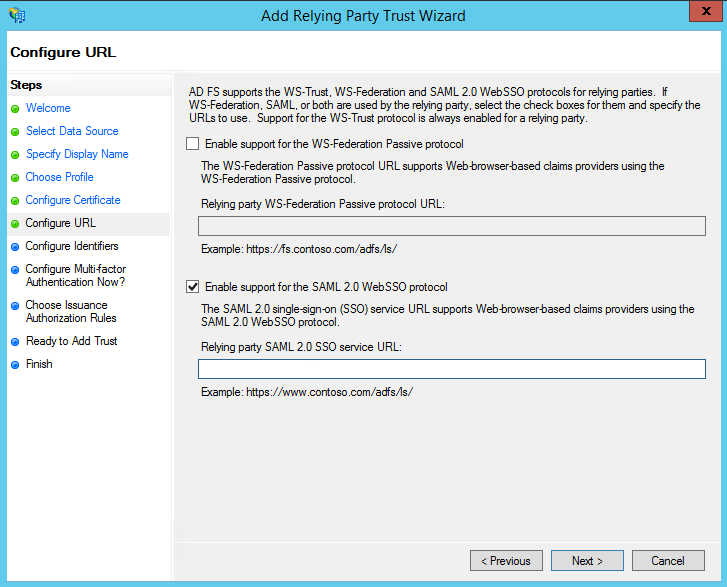
- On the next screen, check the box labeled Enable Support for the SAML 2.0 WebSSO protocol. The service URL will be: https://subdomain.youearnedit.com/saml/acs . Replace subdomain with your KazooHR subdomain. Note: there is no trailing slash at the end of the URL.
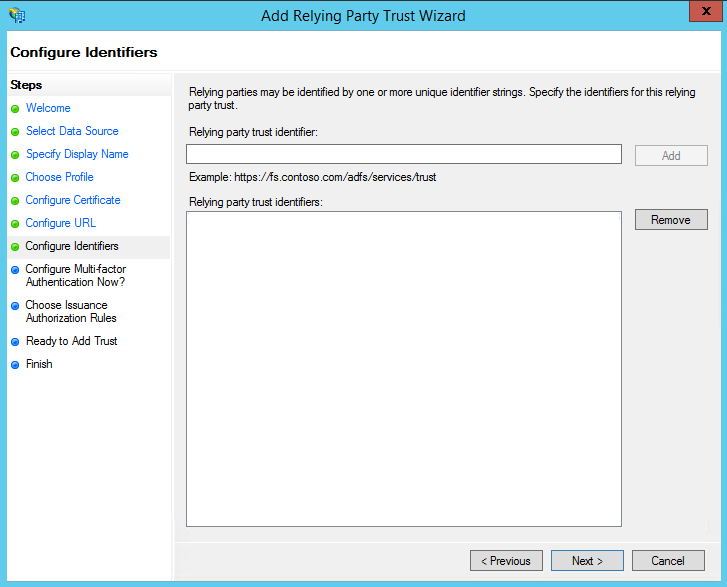
- On the next screen, add a Relying party trust identifier of subdomain.youearnedit.com, replacing subdomain with your YEI subdomain.
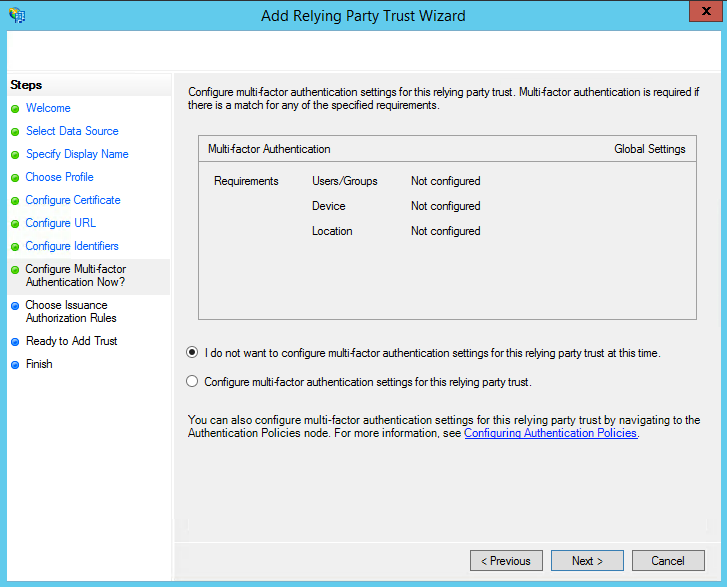
- On the next screen, you may configure multi-factor authentication but this is beyond the scope of this guide.
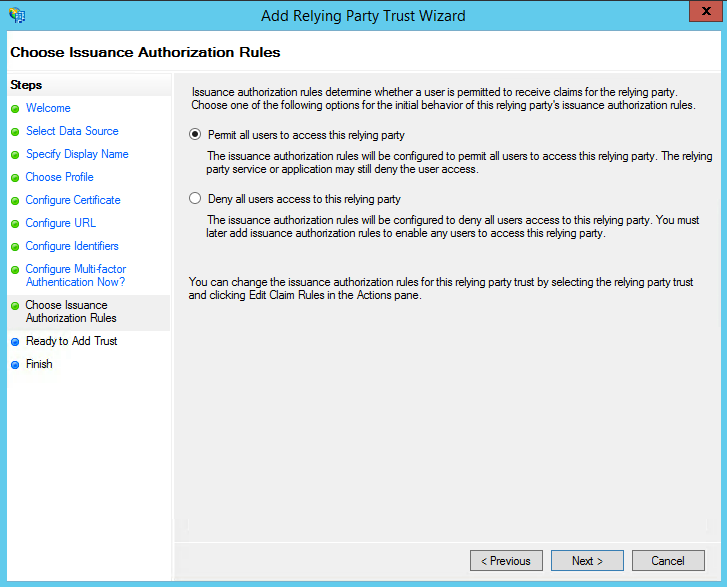
- On the next screen, select the Permit all users to access this relying party radio button.
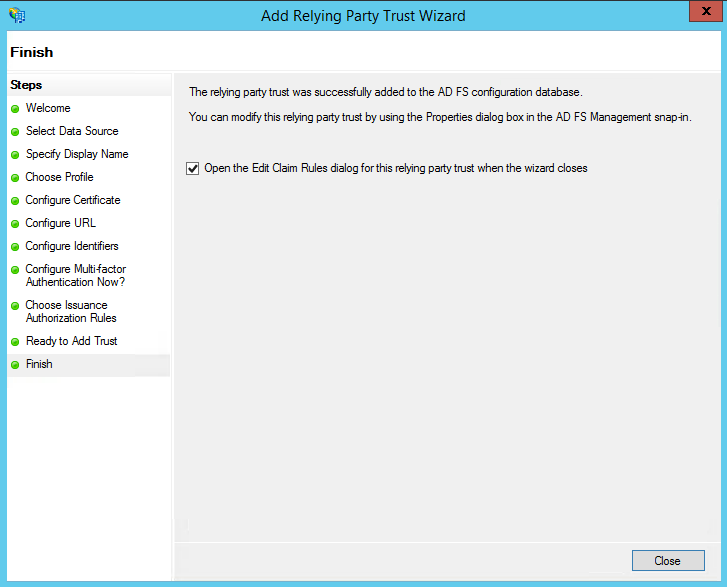
- On the next two screens, the wizard will display an overview of your settings. On the final screen use the Close button to exit and open the Claim Rules editor.
Step 2 - Creating claim rules
Once the relying party trust has been created, you can create the claim rules and update the RPT with minor changes that aren’t set by the wizard. By default the claim rule editor opens once you created the trust.
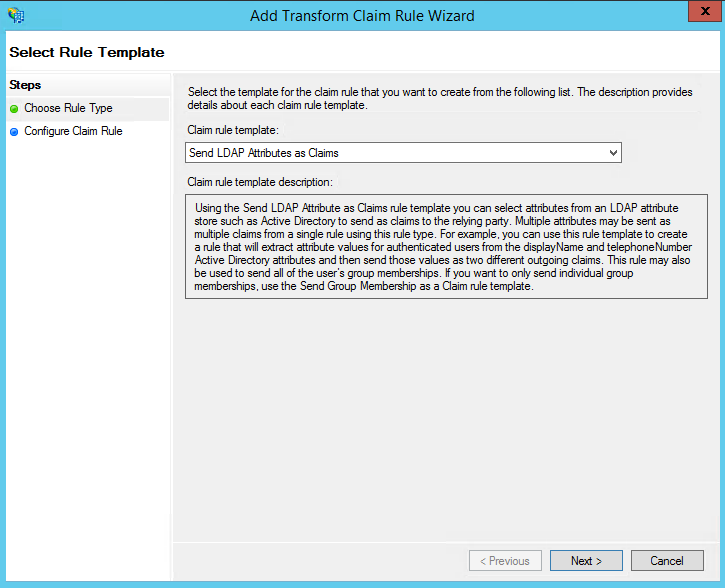
- To create a new rule, click on Add Rule. Create a Send LDAP Attributes as Claims rule.
- On the next screen, using Active Directory as your attribute store, do the following:
- From the LDAP Attribute column, select E-Mail Addresses
- From the Outgoing Claim Type, select E-Mail Address.

-
Click on OK to save the new rule.
-
Create another new rule by clicking Add Rule, this time selecting Transform an Incoming Claim as the template.

- On the next screen:
- Select E-mail Address as the Incoming Claim Type.
- For Outgoing Claim Type, select Name ID.
- For Outgoing Name ID Format, select Email.
- Leave the rule to the default of Pass through all claim values.
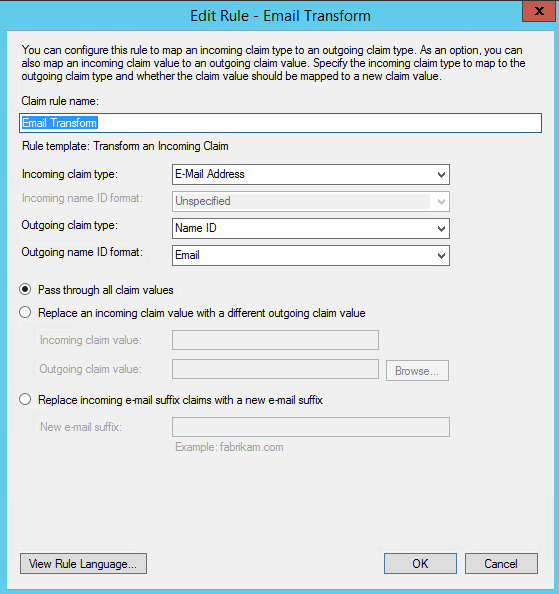
- Finally, click OK to create the claim rule, and then OK again to finish creating rules.
Step 3 - Adjusting the trust settings
You still need to adjust a few settings on your relying party trust. To access these settings, select Properties from the Actions sidebar while you have the RPT selected.
- In the Advanced tab, make sure SHA-256 or SHA-1 is specified as the secure hash algorithm.
- In the Endpoints tab, click on add SAML to add a new endpoint.
- For the Endpoint type, select SAML Logout.
- For the Binding, choose POST.
- For the Trusted URL, create a URL using:
- The web address of your ADFS server
- The ADFS SAML endpoint you noted earlier
- The string ‘?wa=wsignout1.0’
- The web address of your ADFS server
- The URL should look something like this: https://sso.yourdomain.tld/adfs/ls/?wa=wsignout1.0.
- Confirm your changes by clicking OK on the endpoint and the RPT properties. You should now have a working RPT for YEI.
Note: Your instance of ADFS may have security settings in place that require all Federation Services Properties to be filled out and published in the metadata. Check with your team to see if this applies in your instance. If it is, be sure to check the Publish organization information in federation metadata box.
Step 4 - Configuring Kazoo
Once all the above steps have been completed, contact your Kazoo Launch team member or your Account manager. Provide the Federation Metadata URL to YEI and we will get SAML authentication and the SSO certificate set up on the platform.
